The documentation you are viewing is for Dapr v1.9 which is an older version of Dapr. For up-to-date documentation, see the latest version.
Secrets management overview
Applications usually store sensitive information in secrets by using a dedicated secret store. For example, you authenticate databases, services, and external systems with connection strings, keys, tokens, and other application-level secrets stored in a secret store, such as AWS Secrets Manager, Azure Key Vault, Hashicorp Vault, etc.
To access these secret stores, the application imports the secret store SDK, often requiring a fair amount of unrelated boilerplate code. This poses an even greater challenge in multi-cloud scenarios, where different vendor-specific secret stores may be used.
Secrets management API
Dapr’s dedicated secrets building block API makes it easier for developers to consume application secrets from a secret store. To use Dapr’s secret store building block, you:
- Set up a component for a specific secret store solution.
- Retrieve secrets using the Dapr secrets API in the application code.
- Optionally, reference secrets in Dapr component files.
Features
The secrets management API building block brings several features to your application.
Configure secrets without changing application code
You can call the secrets API in your application code to retrieve and use secrets from Dapr supported secret stores. Watch this video for an example of how the secrets management API can be used in your application.
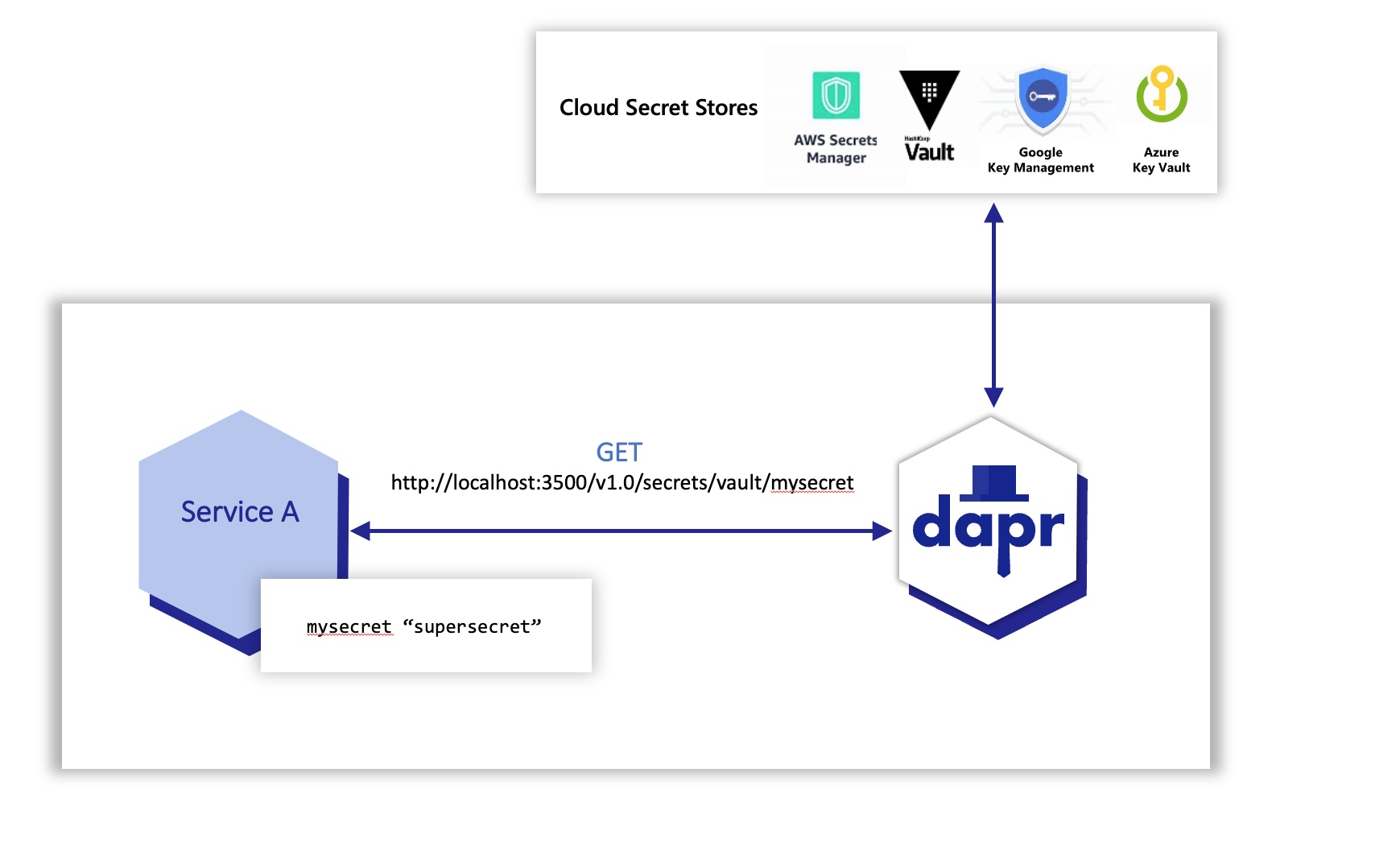
For example, the diagram below shows an application requesting the secret called “mysecret” from a secret store called “vault” from a configured cloud secret store.
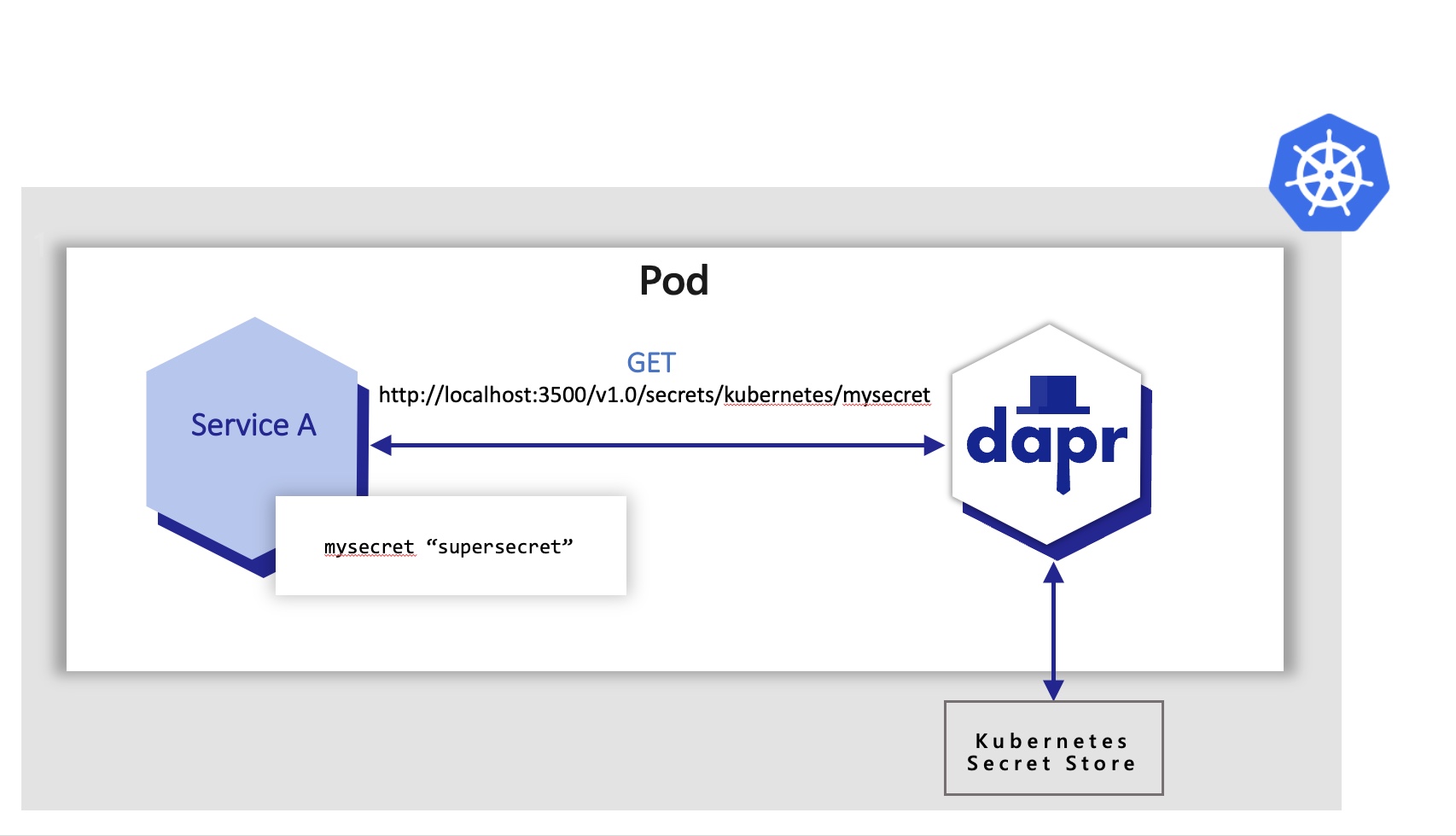
Applications can also use the secrets API to access secrets from a Kubernetes secret store. By default, Dapr enables a built-in Kubernetes secret store in Kubernetes mode, deployed via:
- The Helm defaults, or
dapr init -k
If you are using another secret store, you can disable (not configure) the Dapr Kubernetes secret store by setting disable-builtin-k8s-secret-store to true through the Helm settings. The default is false.
In the example below, the application retrieves the same secret “mysecret” from a Kubernetes secret store.
In Azure, you can configure Dapr to retrieve secrets using managed identities to authenticate with Azure Key Vault. In the example below:
- An Azure Kubernetes Service (AKS) cluster is configured to use managed identities.
- Dapr uses pod identities to retrieve secrets from Azure Key Vault on behalf of the application.
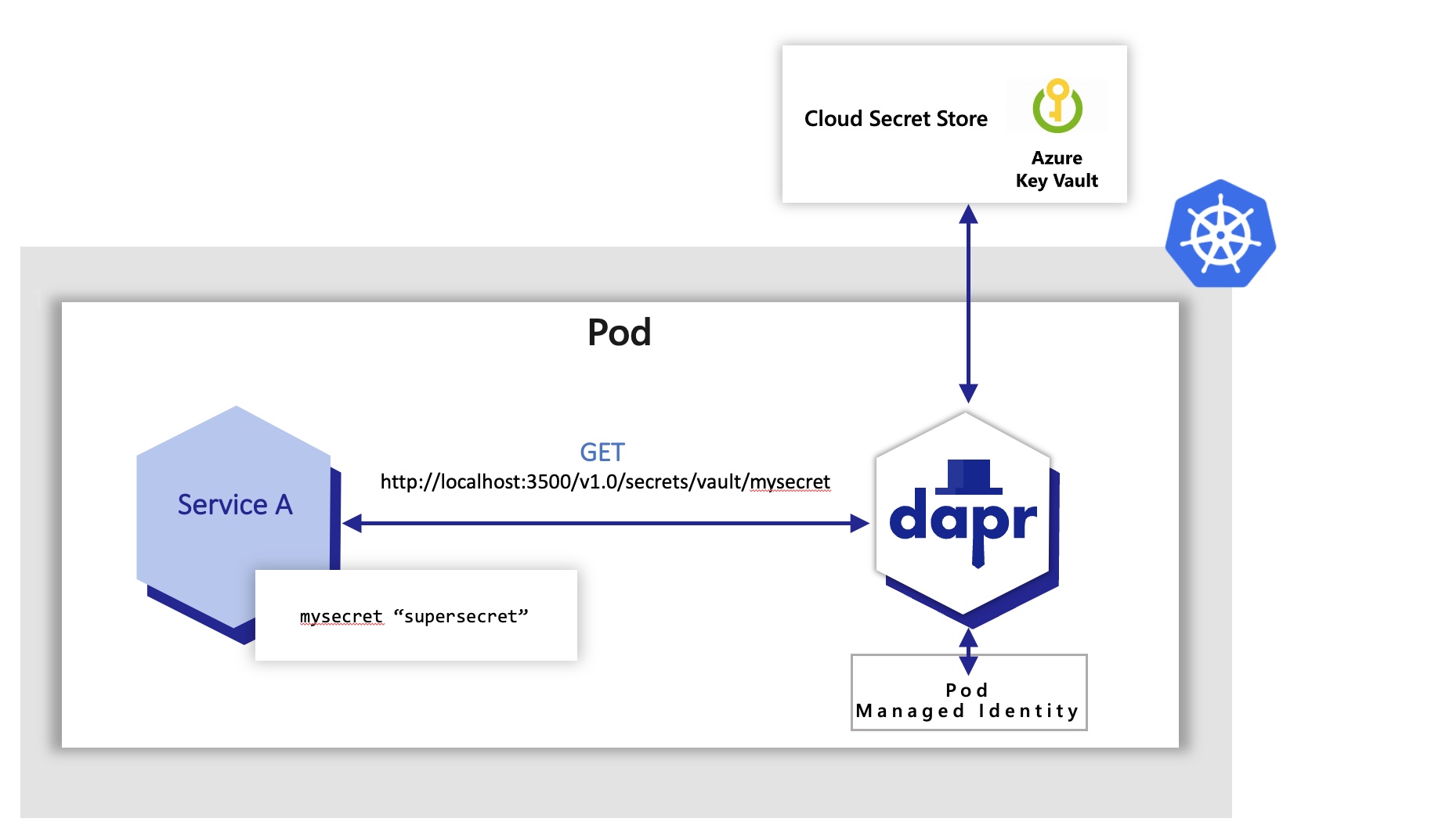
In the examples above, the application code did not have to change to get the same secret. Dapr uses the secret management components via the secrets management building block API.
Try out the secrets API using one of our quickstarts or tutorials.
Reference secret stores in Dapr components
When configuring Dapr components such as state stores, you’re often required to include credentials in components files. Alternatively, you can place the credentials within a Dapr supported secret store and reference the secret within the Dapr component. This is the preferred approach and recommended best practice, especially in production environments.
For more information, read referencing secret stores in components.
Limit access to secrets
To provide more granular control on access to secrets, Dapr provides the ability to define scopes and restricting access permissions. Learn more about using secret scoping
Try out secrets management
Quickstarts and tutorials
Want to put the Dapr secrets management API to the test? Walk through the following quickstart and tutorials to see Dapr secrets in action:
| Quickstart/tutorial | Description |
|---|---|
| Secrets management quickstart | Retrieve secrets in the application code from a configured secret store using the secrets management API. |
| Secret Store tutorial | Demonstrates the use of Dapr Secrets API to access secret stores. |
Start managing secrets directly in your app
Want to skip the quickstarts? Not a problem. You can try out the secret management building block directly in your application to retrieve and manage secrets. After Dapr is installed, you can begin using the secrets management API starting with the secrets how-to guide.
Next steps
- Learn how to use secret scoping.
- Read the secrets API reference doc.
Feedback
Was this page helpful?
Glad to hear it! Please tell us how we can improve.
Sorry to hear that. Please tell us how we can improve.